How Flubot targets Android phone users and their money
Malware steals login credentials for banking and cryptocurrency apps — and it could spread around the world
Flubot, also called Cabassous, is an Android banking malware (also a banking trojan) that is pushed by cybercriminals in large-scale campaigns, targeting consumers across Europe this spring.
Access to the botnet is being sold in underground forums by the operators to criminal groups as a so-called malware-as-a-service (MAAS). The actors behind the Flubot botnet sending Smishing (SMS phishing) messages with fake notices of upcoming package deliveries and urge the victim to follow a link to track the shipment.
The landing page then presents a download button supposedly required to track the package. After a victim falls for this social engineering trick, Flubot is downloaded to the mobile device and requests various permissions, including access to the contact list, sending SMS messages, and overlaying other applications.
The contact list is subsequently sent to a command-and-control (C&C or C2) server and used to seed new waves of smishing messages that are sent through infected phones (devices).
The Flubot malware does not exploit any vulnerabilities in the Android OS or targeted devices but prompts the user to manually grant two powerful system permissions. These permissions allow the attackers to steal credentials from banking and cryptocurrency apps on infected devices, using overlays and then exfiltrate one-time-password (OTP) and two-factor authentication (2FA) codes.
Campaigns and versions
From late 2020 and into early 2021, an initial Flubot campaign hit Spain and reportedly infected more than 60,000 Android devices. Spanish police investigated and eventually arrested four men suspected of being involved in the campaign.
As mentioned earlier, the Flubot operators had been renting out the botnet, so the suspects arrested in Spain are likely just “customers” of the actual Flubot operators, trying to monetize access to victims’ mobile phones. This is further evidenced by the fact that new campaigns against additional countries started to emerge soon after.
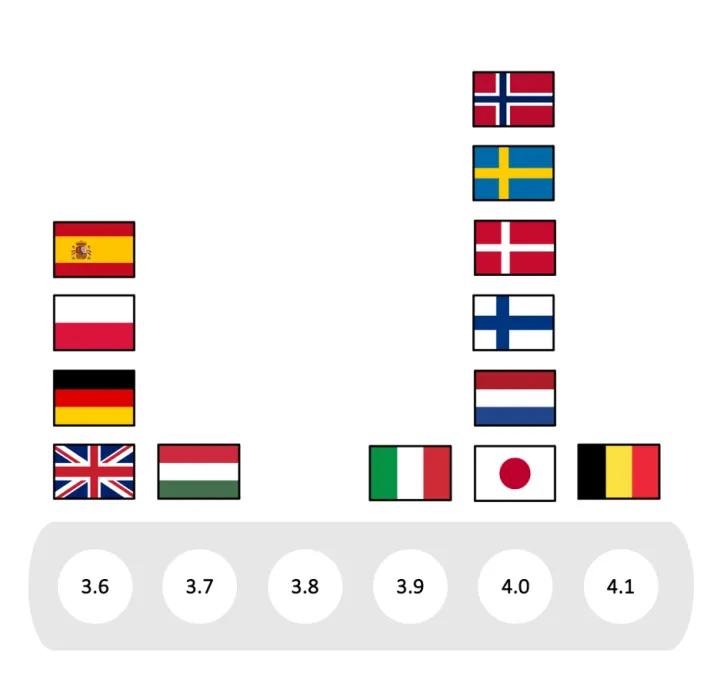
The Flubot developers have been busy adding support for new target countries to the malware as shown for version 3.6 to 4.1 in the visualization below.
The screenshot below shows an example of a SMS message targeting German users to lure them into following a link to track a fictitious package shipment:
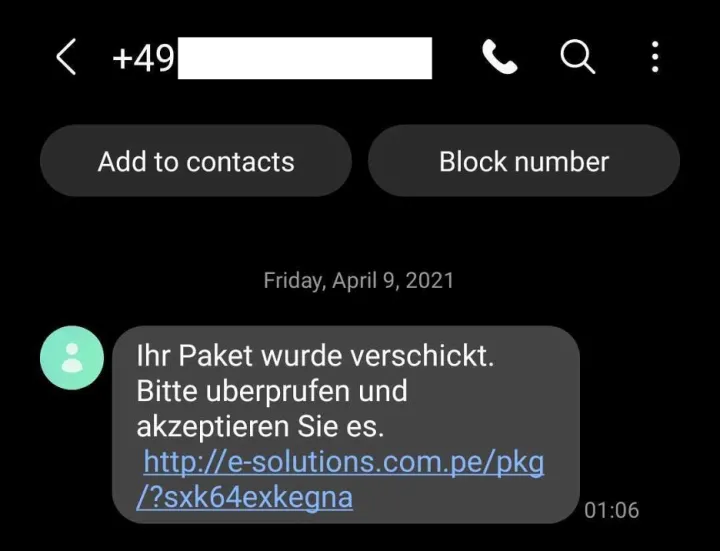
In some cases, the messages include the name of the recipient-— likely crafted using stolen contact-list data from previous victims.
The respective links lead to country-specific landing pages, as can be seen in the comparison of DHL-themed download sites below:
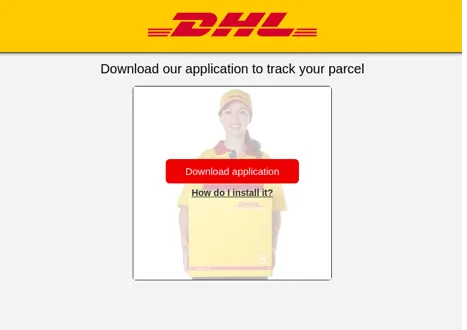




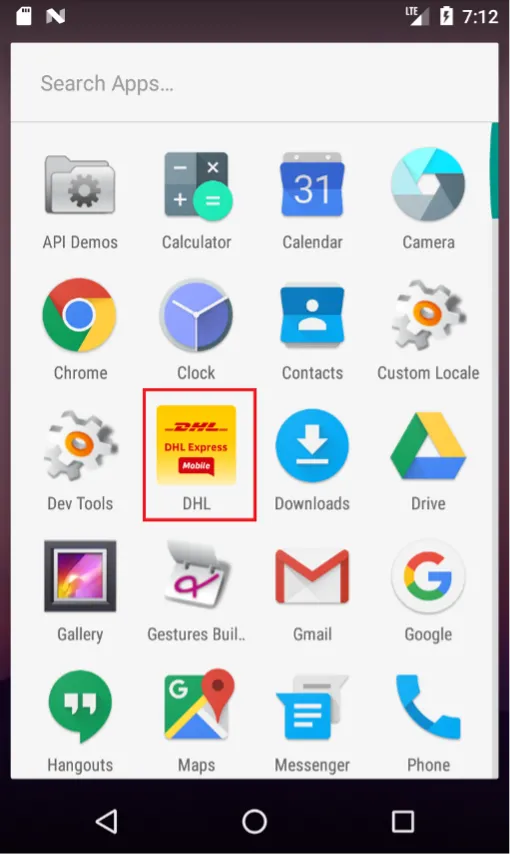
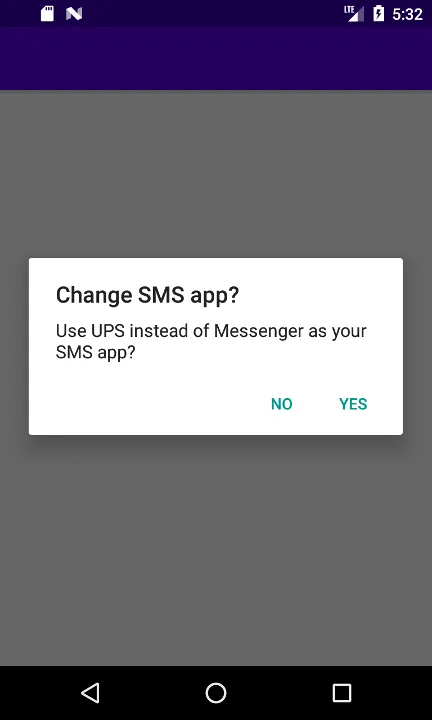
There are different variants of the Flubot app that disguise themselves by using the brand names of package delivery services like DHL, FedEx, UPS, or the Spanish postal service Correos.
Statistics
Norton Labs researchers analyzed the telemetry of our mobile protection technologies to measure the prevalence of Flubot affecting our customers. The chart below shows the total number of attempted installations of Flubot in blue. The orange line represents Flubot lure SMS messages as a percentage of total blocked SMS messages from unknown senders for the respective day.
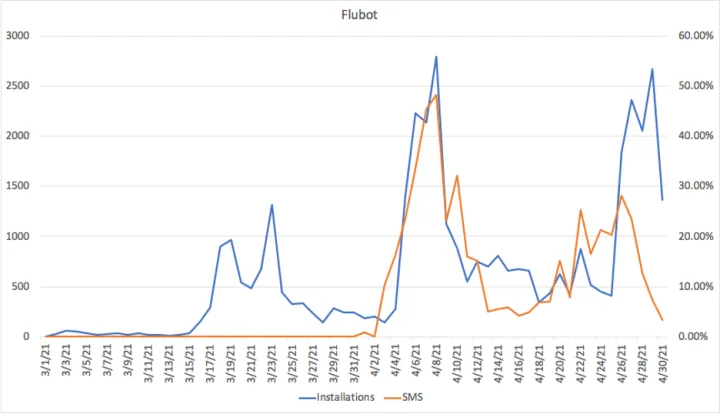
The second wave of attempted Flubot installations in our statistics from around April 4 to April 11 coincides with the campaign in Germany. The third wave of attempted installations at the end of April corresponds with the start of the Flubot campaign targeting mobile phone numbers in the UK. The related smishing attacks (orange line) peaking a few days earlier.
Shown below are metrics from sinkholing efforts (as provided by Shadowserver on May 11 (and previously on April 27) for seeds 1136, 1642, 1813, 1905, 1949, and 2931. These efforts show a decline in infections (Refer to the table of countries and seed values below). As with many sophisticated malware families, it’s reasonable to expect an ebb and flow in the infection (and detection) rates as sinkholing and mitigation efforts are leapfrogged by the operator’s improvements.

Analysis
The Flubot malware continues to evolve through active development since its introduction to the cybercrime underground. Especially since March of 2021, several versions were released ranging from 3.5 to 4.1. Even for samples with the same version number, our analyses revealed differences and the addition of new features. The research described in this section is the result of analyzing variants of Flubot version 4.0 that only differed in the list of targeted countries but not in functionality.
Permissions
Flubot requests an extensive list of Android permissions through the system dialog upon installation:
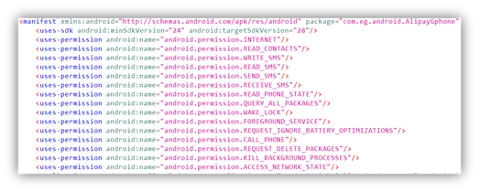
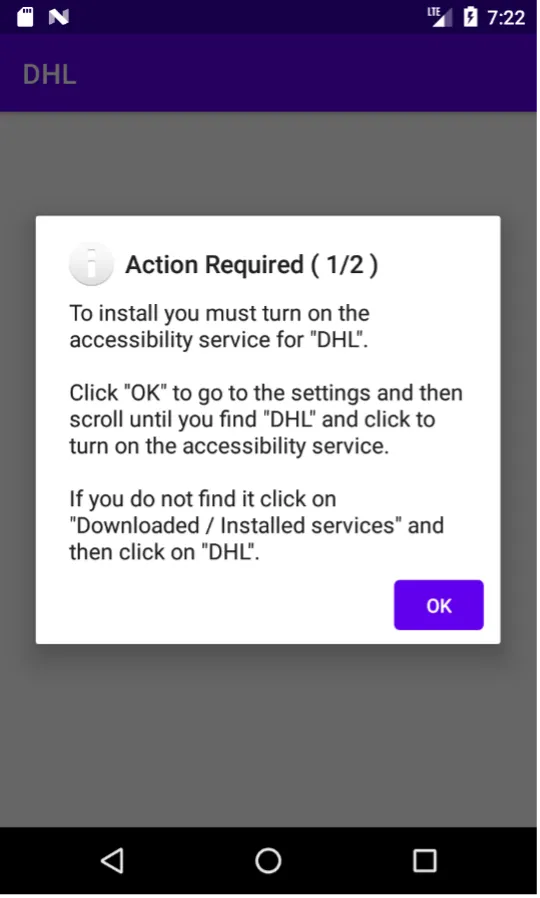
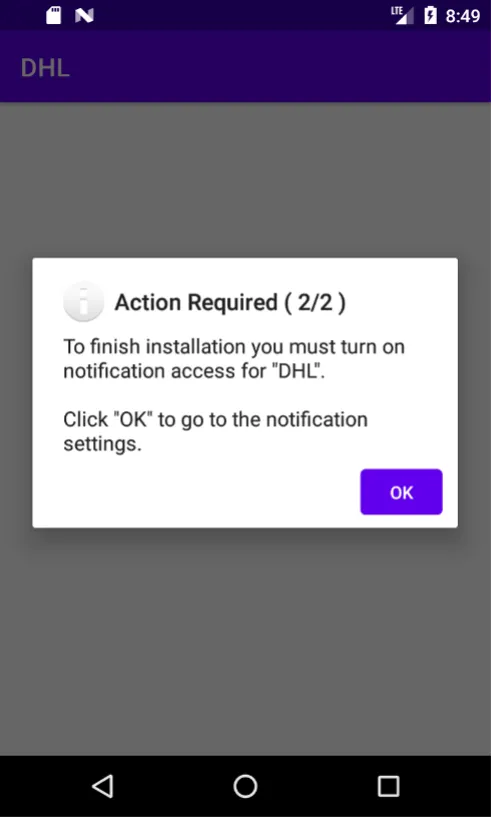
Once the app is executed, it prompts the user to grant two additional permissions by following instructions to manually allow “Accessibility Service” and “Notification Access” through the phone’s system settings.
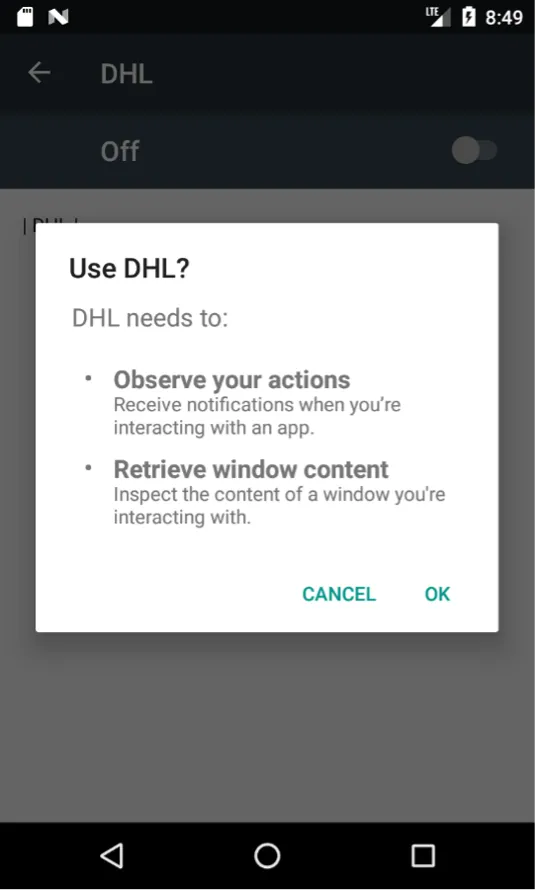
Below screenshots show the app prompting the user to enable the “Accessibility Service” and its respective setting screen. The Android “Accessibility Service” is supposed to allow apps to assist users with disabilities. This app setting grants powerful permissions to control what is shown on the phone display and to intercept user input. Several Android malware families have integrated prompts to socially engineer the user into willfully enabling the accessibility setting to then use it for keylogging of credentials and overlay app screens (see below).
In the next step, the user is prompted to also enable “Notification Access” for the app in the corresponding system dialog.
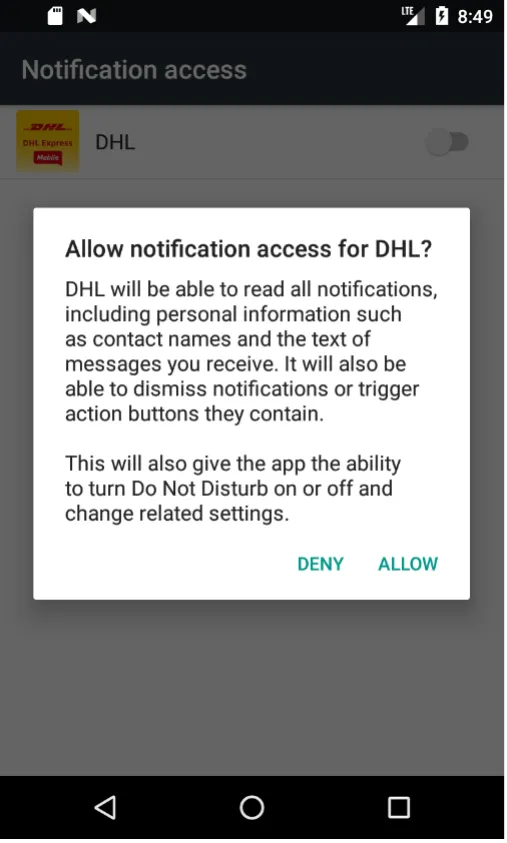
Flubot will use the “Accessibility Service” permission to register as the default messaging app on the phone. This allows the malware to quietly send and intercept SMS messages and thus capture OTPs used in online banking.
Overlays
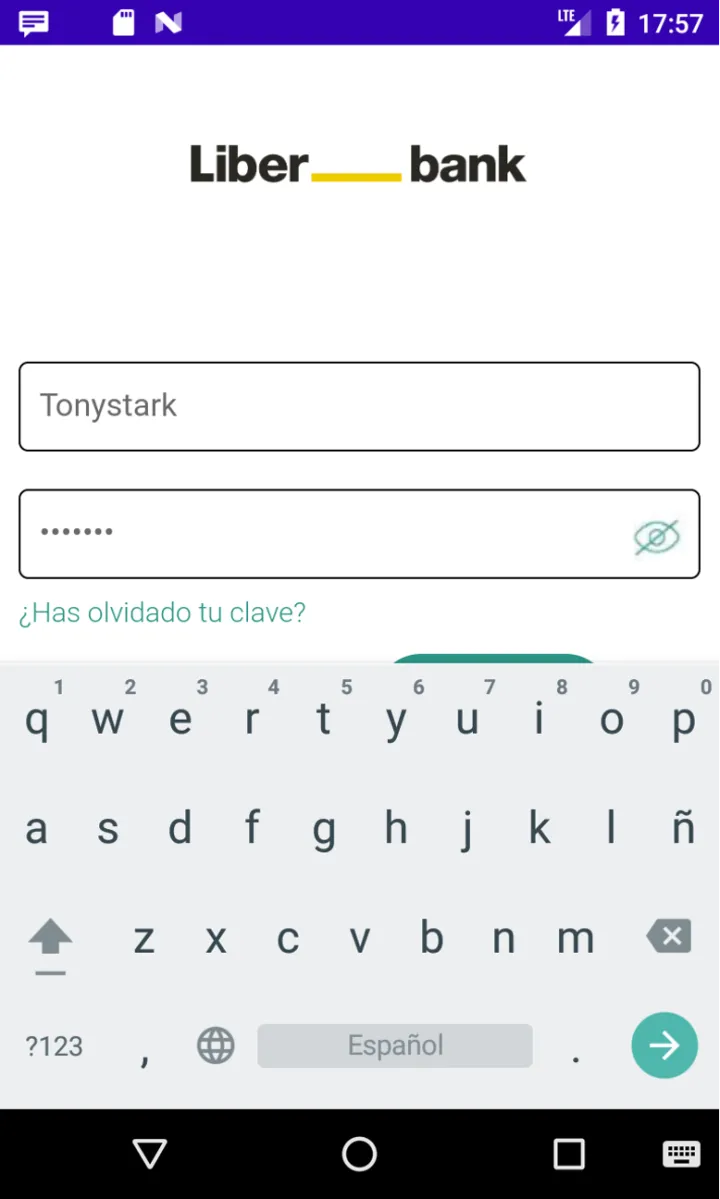
The main functionality of the Flubot mobile banking trojan is to steal login credentials for banking and cryptocurrency apps running on the phone. The malware achieves this using the previously mentioned permissions and abusing existing Android APIs.
After installation, it will send a list of installed applications that the C2 server matches to a list of package names targeted by the cybercriminals. Flubot will then download specifically crafted HTML pages that will be displayed as an “overlay” when the respective app is started. When the user then enters their credentials, they interact with Flubot instead of the banking app and their credentials are harvested.
The following screenshot shows an overlay captured on an infected analysis device that intercepts the login for Spanish Liberbank:
Domain generation algorithm
Instead of using a static list of C2 servers, the developers added a domain generation algorithm (DGA) to Flubot. Early versions Flubot generated a list of 2,000 domains each month, while the most recent version 4.0 can generate up to 5,000 domains. When generating the domains, the algorithm alternates between appending the top-level domains .ru (Russia), .su (Senegal), and .cn (China). This is notable, because it is more difficult for network operators to sinkhole domains in these top-level domains.
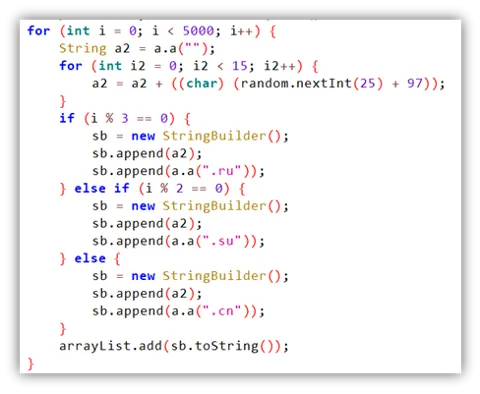
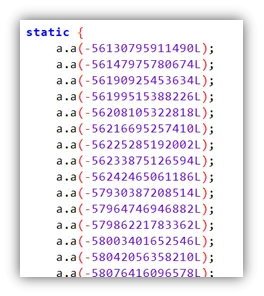
The algorithm calculates the initialization value for the random number generator in the function above using two parameters: the year/month and a static seed value.
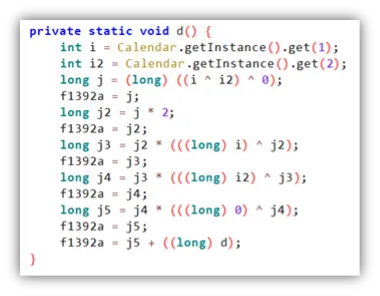
Until Flubot version 3.7 the seed value remained static, while later versions include different seed values depending on the country code of the infected Android phone as shown in the screenshot below:
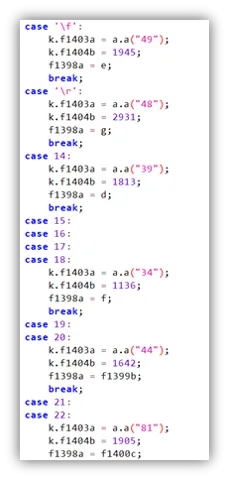
The current list of countries and seed values for Flubot in the analyzed variants are as follows:
| Prefix | Country | Seed Value |
|---|---|---|
| +34 | Spain | 1136 |
| +48 | Poland | 2931 |
| +49 | Germany | 1945 |
| +39 | Italy | 1813 |
| +44 | United Kingdom | 1642 |
| +81 | Japan | 1905 |
| +31 | Netherlands | 2931 |
| +45 | Denmark | 2931 |
| +358 | Finland | 2931 |
| +46 | Sweden | 2931 |
| +47 | Norway | 2931 |
| +32 | Belgium | 2931 |
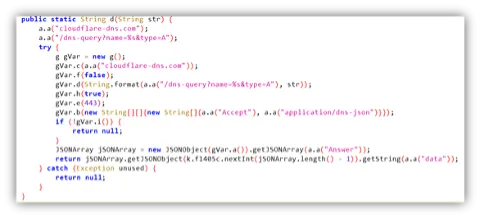
After generating the DGA domains, the malware will iterate through the list and try to resolve each entry to an IP. While early versions of Flubot used the DNS service configured in the phone, recent versions have switched to utilize encrypted DNS-over-HTTPS services from Cloudflare and Google.
The communication from the C2 to the Flubot malware is encrypted using an XOR operation with a static key. Communication in the opposite direction, from the malware to the C2, uses RSA Public Key Infrastructure (PKI) to encrypt the data. This also doubles as a protection mechanism to prevent researchers or competitors from taking over the botnet via C2. While the C2 is protected through this PKI scheme, sinkholing predicted DGA domains is still possible.

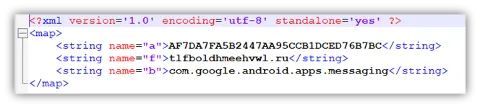
The malware also generates a random “Bot ID” and retrieves device information such as Device ID and manufacturer details which is then submitted to the botnet during communication with the C2 server. The “Bot ID” and the first working DGA domain will then be stored in an XML configuration file:
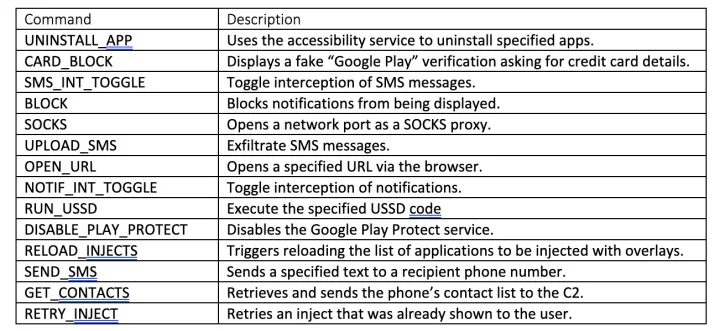
Botnet commands
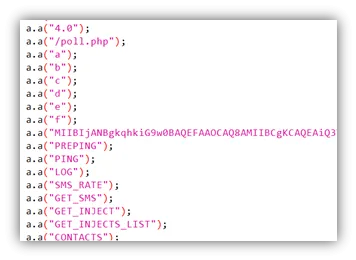
When communicating with the C2 server, the botnet can respond with the following list of commands:
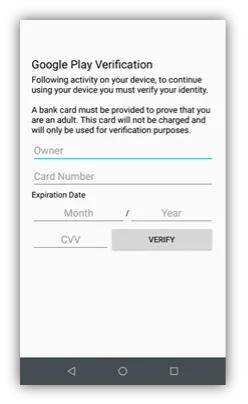
Besides the overlays targeting specific applications, the malware also has a generic mechanism to steal credit card information through social engineering. This is triggered by a “CARD_BLOCK” command from the C2 server and displays a “Google Play Verification Window” as shown below:
Evasion
The Flubot developers are using a custom packer and evasion mechanisms to complicate detection and analysis of the malware. The main application is packed and stored under the filename “assets/classes-v1.bin.” Once the app is executed, it unpacks the malware into “app_apkprotector_dex/classes-v1.dex” of the application’s data directory. In addition, text strings in the unpacked file are obfuscated likely using the opensource string obfuscator framework Paranoid1.
The screenshots below show a list of strings in Flubot before and after manual de-obfuscation:
Version 4.1
Shortly before the publication of this report, a version 4.1 of Flubot was discovered. However, the analysis described above still apply to the new version as well.
Summary & Outlook
Mobile banking trojans like Flubot are becoming more popular among cybercriminals as more consumers than ever before rely on mobile devices for internet banking, access to financial services, and e-commerce. The Flubot malware is in active development and is likely to continue to spread throughout the world as support for new regions and functionality is implemented in future versions.
Flutbot can circumvent security controls by tricking the end-user into giving powerful system permissions. Better user awareness training is key to combatting this type of attack:
-
Only install applications from trusted sources like the Google Play store.
-
Only grant permissions to trusted applications and understand what capabilities that permission is granting before accepting them.
Indicators
Example hashes of analyzed Flubot variants:
-
74183f6454d2aaa44fcb363eb71beb33f04845c7fe4b402d06a87bab7b99e235
-
5c3384bfeb479db3f1ed98578c80d1e3859640ea7cbfe62fbaa9634118cf4636
-
5c9057d6d19f82fbba255d58e9b0da7102fed08ee25e548e08f0a5b22efc42a2
Active C2 domains:
-
iixoqoiphdhkdbq[.]ru
-
pvvbjvedsmjphil[.]ru
-
tlfboldhmeehvwl[.]ru
Package names used in early Flubot versions:
-
com.iqiyi.i18n
-
com.eg.android.AlipayGphone
-
com.tencent.mm
-
com.tencent.mobileqq
-
com.taobao.taobao
Innovations from Norton Labs are for research, evaluation, and consumer feedback purposes. NortonLifeLock does not give any warranties as to the suitability or usability of these prototypes and recommends safeguarding data and reviewing all terms and conditions before use.
Copyright © 2021 NortonLifeLock Inc. All rights reserved. NortonLifeLock, the NortonLifeLock Logo, the Checkmark Logo, Norton, LifeLock, and the LockMan Logo are trademarks or registered trademarks of NortonLifeLock Inc. or its affiliates in the United States and other countries.









We encourage you to share your thoughts on your favorite social platform.